[Day 15] Cisco ISE Mastery Training: Validating RADIUS & TACACS+ Connectivity
Table of Contents
Introduction
Validation is the bridge between configuration and confidence. After you add devices, policies and profiles in Cisco ISE, the next critical step is to prove RADIUS and TACACS+ traffic flows end-to-end and that ISE is making the expected authentication/authorization decisions. This lesson gives you exact GUI click paths, device CLI tests, packet-capture tips, and a prioritized troubleshooting checklist so you and your students can validate connectivity reliably — not guess.
Problem Statement
Common real-world symptoms that indicate failed RADIUS/TACACS+ connectivity:
- Switch/WLC sends requests but ISE shows nothing in Live Logs (no arrival).
- ISE receives Access-Request but immediately rejects (shared secret mismatch, identity lookup error, wrong policy).
- TACACS+ logins fail or commands are not accounted for.
- Intermittent failures under load — devices time out or retry.
These can be caused by network (routing/NAT/ACL), protocol (wrong port/UDP vs TCP), device config (wrong source IP, secret), or ISE problems (service down, identity store unreachable). The goal: isolate layer by layer and verify.
Solution Overview
We validate RADIUS and TACACS+ connectivity by systematically checking:
- Basic IP reachability & name resolution (ping / nslookup).
- Transport connectivity (TCP/49 for TACACS+, UDP 1812/1813 for RADIUS).
- Correct NAD entry in ISE (IP matches RADIUS source).
- Shared secret correctness and matching ports.
- ISE service health and Live Logs for incoming messages.
- End-to-end auth tests from the NAD (test aaa) and from a test client (802.1X/MAB).
- Packet captures on ISE (tcpdump) and NAD (if available) to prove packets arrived and responses sent.
Follow the step sequence below — it’s linear and designed so each step eliminates an entire class of problems.
Sample Lab Topology
Platform: VMware ESXi or EVE-NG
Nodes / IPs (example)
- ISE (PAN+PSN):
10.10.10.50— TACACS+/RADIUS - Switch (NAD, IOSv/L2):
10.10.10.2— RADIUS/TACACS client - WLC (optional):
10.10.10.20 - Active Directory (optional):
10.10.10.10 - Admin / Test client:
172.16.1.10
Topology Layout:
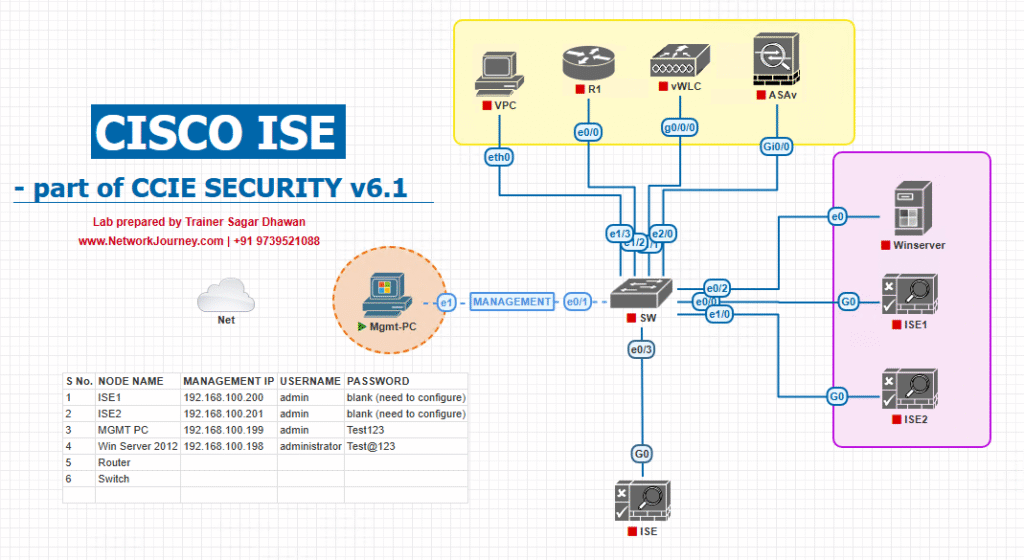
Notes: Ensure ISE + NADs are on routable networks, DNS resolves FQDNs if you used FQDNs for devices, and NTP is synchronized (time matters for certs/EAP).
Step-by-Step GUI Configuration Guide (with CLI validation)
Follow these numbered steps. After each step run the listed CLI/GUI checks.
PRE-CHECKS (run first on ISE console)
# From ISE ise/admin# ping 10.10.10.2 # reach NAD ise/admin# ping 10.10.10.10 # reach AD (if used) ise/admin# nslookup ad.lab.local 10.10.10.10 ise/admin# show ntp status ise/admin# show application status ise # ensure services running ise/admin# show version
If these fail, stop and fix network/DNS/NTP before continuing.
Step 1 — Confirm Network Device Entry in ISE (GUI)
- ISE GUI → Administration → Network Resources → Network Devices.
- Locate the NAD (switch/WLC) and verify:
- IP address matches the NAD’s RADIUS source IP.
- Shared secret is set (recorded elsewhere; ISE will not reveal it).
- Correct RADIUS ports shown (1812/1813).
[Screenshot: Administration → Network Resources → Network Devices → NAD entry]
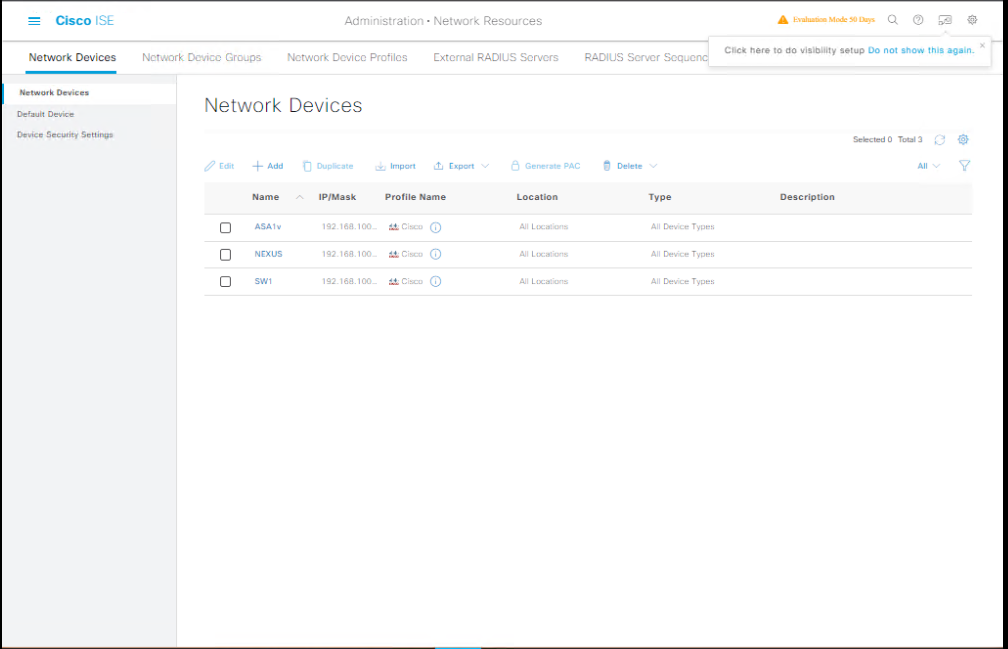
Validation: If source IP is wrong (NAD sends from different interface), add that IP or fix device routing.
Step 2 — Test Transport Connectivity (ports)
From a jump host / admin PC:
# TCP check (TACACS+) nc -vz 10.10.10.50 49 # expect "succeeded" for TCP/49 # UDP is connectionless; check RADIUS with radclient or nmap: # Using radclient on Linux to send a simple Access-Request: echo "User-Name=test,User-Password=badpass" | radclient -x 10.10.10.50:1812 auth sharedsecret # radclient will show if ISE responded (Access-Reject/Access-Accept)
If TCP/49 fails: firewall/ACL issue. If radclient times out: UDP blocked or ISE not listening.
Step 3 — Quick NAD side test (IOS) — send a real auth
On Cisco IOS switch:
# Simulate a username/password request to configured radius server test aaa group radius ISE-GROUP username test password test123 new-code
- Watch ISE Operations → RADIUS → Live Logs (or TACACS Live Logs for TACACS) for request arrival and result.
- If test fails with no response, check NAD
show run | section radiusand source interface.
IOS show commands to validate:
show running-config | section radius show aaa servers show ip interface brief # check source IP routes
Step 4 — Validate TACACS+ auth from device (IOS)
# Syntax can vary; example: test aaa group tacacs+ admin <username> <password> legacy
- Check ISE: Work Centers → Device Administration → Live Logs.
- Expect to see authentication event, authorization profile applied, and if accounting enabled, commands logged.
Step 5 — Capture packets on ISE (prove arrival) — lab only
RADIUS capture
# Capture RADIUS auth/acc packets ise/admin# tcpdump -i eth0 -s 0 -w /tmp/radius.pcap 'udp port 1812 or udp port 1813' # Reproduce auth from NAD; Ctrl+C when done # Copy /tmp/radius.pcap and open in Wireshark to verify Access-Request & Access-Accept
TACACS+ capture
ise/admin# tcpdump -i eth0 -s 0 -w /tmp/tacacs.pcap 'tcp port 49'
What to look for in capture:
- Source IP equals NAD management IP; Access-Request present; ISE responds Access-Accept or Access-Reject. If request present but no response — ISE process crashed or service not bound to expected interface.
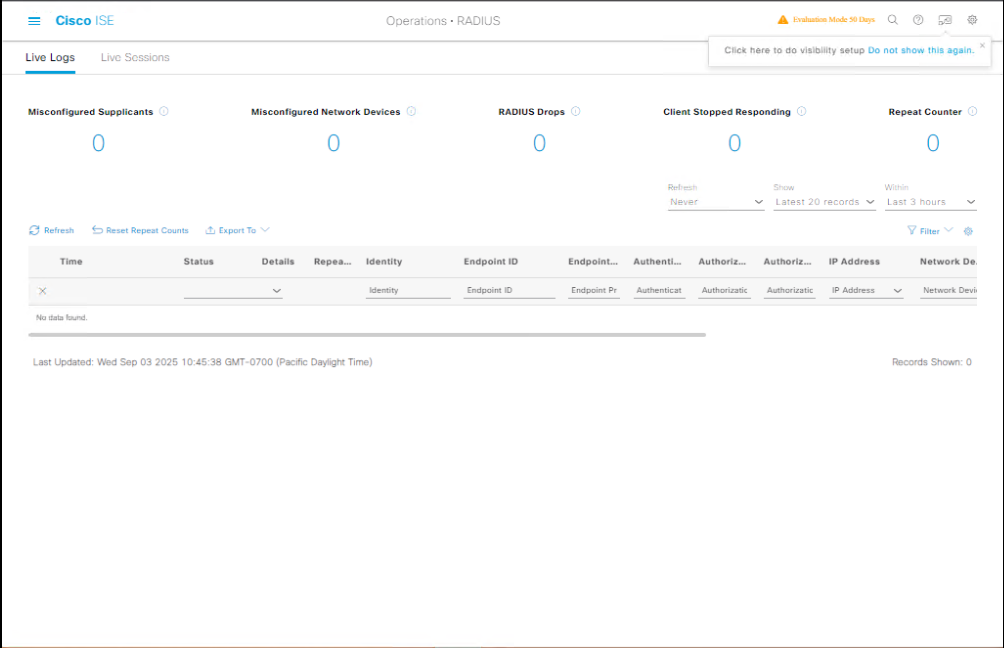
Step 6 — Check ISE Live Logs & Message Details (GUI)
- ISE GUI → Operations → RADIUS → Live Logs → filter by NAS IP (switch) or username.
[Screenshot: Operations → RADIUS → Live Logs] - Click the event → expand details: Authentication source, Identity Source Sequence, Authorization Profile, Returned Attributes (Tunnel-Private-Group-ID, Filter-ID).
- For TACACS+: Work Centers → Device Administration → Live Logs (same idea).
[Screenshot: Device Administration → Live Logs]
Validation: Live Logs show which policy matched and why. If policy hit is wrong, edit policy and retest.
Step 7 — Validate 802.1X end-to-end (client test)
- On test client: enable 802.1X supplicant (PEAP/MSCHAPv2 or EAP-TLS).
- Connect to the switch port.
- Observe on switch:
show authentication sessions interface Fa0/1 show dot1x all
- Observe on ISE Live Logs for Access-Request (EAP) and Access-Accept. Confirm VLAN/dACL in attributes.
If EAP fails: check certificates (server cert on ISE, trust on client), and ensure time sync.
Step 8 — Check TACACS+ command accounting (if enabled)
- Ensure on switch you have
aaa accounting commands 15 default start-stop group tacacs+. - On ISE GUI: Work Centers → Device Administration → TACACS Accounting (or Live Logs) → search by user/device/time.
- You should see session start/stop and commands executed.
CLI check on switch: not all platforms show per-command accounting locally, but you can show accounting or look for logs.
Step 9 — Common quick fixes (if tests fail)
- No packets seen in ISE tcpdump: fix routing, NAT, firewall. Confirm NAD sends from management IP.
- Packets seen but Access-Reject: check shared secret, username/password, identity source sequence.
- ISE shows “Client not found” or “Client IP mismatch”: NAD RADIUS source IP differs — update ISE Network Device list.
- TACACS+ login rejects with “authorization failed”: check command set mapping and AD group membership.
- Intermittent failures under load: increase NAD timeout/retries and add an additional PSN for redundancy.
Step 10 — Document & Automate
- Save a checklist for each NAD: IP, secret, source interface, expected ports, test username.
- Automate basic port checks (
nc,radclient) in your CI lab scripts so students can validate quickly.
FAQs
1. How can I confirm if my RADIUS requests are reaching Cisco ISE?
- GUI: Navigate to Operations > RADIUS > Live Logs in ISE and look for incoming authentication attempts.
- CLI: Use
debug radius allon the network device to check outgoing requests.
2. What’s the best way to test TACACS+ connectivity without impacting production traffic?
- Create a dedicated TACACS+ test account with limited permissions and use
test aaa group tacacs+ <username> <password>from the device CLI.
3. How do I verify that both authentication and authorization are successful for RADIUS?
- In the ISE GUI, check Live Logs for “Authentication Succeeded” and “Authorization Succeeded” messages.
- Ensure the correct policy set is applied by reviewing Operations > RADIUS > Live Logs > Details.
4. Which TCP/UDP ports should I check if connectivity fails?
- RADIUS uses UDP 1812 (auth) & 1813 (acct).
- TACACS+ uses TCP 49.
- Use
telnet <ISE_IP> <port>from the device to confirm port accessibility.
5. Can I test RADIUS and TACACS+ from the ISE CLI itself?
- No direct test from ISE CLI, but you can run
pingandnslookupto ensure DNS/IP reachability, and check logs for inbound requests.
6. My TACACS+ test passes on CLI but fails in ISE—what could be wrong?
- Possible causes: wrong shared secret, incorrect device IP in ISE’s Network Devices, or missing TACACS+ Services enablement in Administration > Deployment.
7. How do I see if the correct authorization profile is being applied?
- In the ISE Live Logs, click on the specific session → Details. Check the Authorization Policy Matched field.
8. What CLI command verifies that my switch or router is actually sending TACACS+ requests?
debug tacacs eventsordebug tacacs packeton IOS/IOS-XE devices.
9. Why does my RADIUS test fail when using domain credentials?
- Ensure ISE is joined to the correct Active Directory domain, the AD connector is active, and the policy set matches domain user authentication rules.
10. How do I ensure my test results are accurate before applying in production?
- Use a dedicated lab switch/WLC in EVE-NG/VMware connected to ISE.
- Validate using both CLI (
test aaa) and GUI (Live Logs) to confirm bidirectional verification.
YouTube Link
For more in-depth Cisco ISE Mastery Training, subscribe to my YouTube channel Network Journey and join my instructor-led classes for hands-on, real-world ISE experience
Closing Notes (Key takeaways)
- Validate in layers: network → transport → device config → ISE service → policy.
- ISE Live Logs and packet captures are your two best friends for proving connectivity.
- Always confirm NAD source IP and shared secret — most failures trace back here.
- Automate the basic checks in labs so students can rapidly validate changes and learn from failures.
- Document test accounts & expected results for reproducible validation across class sessions.
Fast-Track to Cisco ISE Mastery Pro
Want systematic lab workflows, real-world troubleshooting recipes, and live guided practice so you can actually deploy ISE at scale? I run a focused 4-month instructor-led CCIE Security & ISE Mastery program — weekly live labs (VMware/EVE-NG), graded lab reviews, 1:1 doubt sessions, and exam-grade scenarios.
• Free eligibility & lab review call for qualified applicants — submit your lab topology and get a personalized roadmap.
• Limited seats to keep batches hands-on.
Reserve your spot / get the course outline: https://course.networkjourney.com/ccie-security/
Enroll Now & Future‑Proof Your Career
Email: info@networkjourney.com
WhatsApp / Call: +91 97395 21088
![[Day 15] Cisco ISE Mastery Training: Validating RADIUS & TACACS+ Connectivity](https://networkjourney.com/wp-content/uploads/2025/08/Day-15-Cisco-ISE-Mastery-Training-Validating-RADIUS-TACACS-Connectivity.png)
![[Day 38] – Cisco ISE Mastery Training: Wired Supplicant Configuration for Windows](https://networkjourney.com/wp-content/uploads/2025/08/Day-38-–-Cisco-ISE-Mastery-Training-Wired-Supplicant-Configuration-for-Windows.png)