[Day 25] Cisco ISE Mastery Training: Dynamic VLAN Assignment in Wired Networks
Table of Contents
Introduction
Dynamic VLAN Assignment (DVA) is a cornerstone capability in Cisco Identity Services Engine (ISE) deployments for wired networks. In traditional environments, VLANs are statically configured on switch ports — meaning every port is tied to a single network segment regardless of who plugs in. This “one-size-fits-all” approach creates security blind spots, limits agility, and forces manual reconfiguration when users, devices, or policies change.
With Cisco ISE, VLAN assignment becomes context-driven. Instead of static port configurations, VLANs are assigned dynamically based on user identity, device type, posture compliance, location, or security group. When a wired endpoint connects, ISE determines who/what it is and instructs the switch to place it into the correct VLAN automatically, without touching the switch configuration.
This enables true zero-touch access control, reduces operational overhead, improves security posture, and supports BYOD, IoT, and contractor onboarding without IT intervention.
Problem Statement
In static VLAN setups:
- Operational overhead: Every move/add/change requires physical switch configuration changes.
- Security risk: Non-compliant or rogue devices can get full network access if plugged into an active port.
- Inflexibility: VLAN assignment is based on where you connect, not who/what you are.
- Poor BYOD/IoT handling: Different device types with different access requirements often share the same VLAN.
- Guest onboarding delays: IT staff must manually configure guest VLANs per port.
In large enterprise campuses with thousands of ports, this model is inefficient and error-prone.
Solution Overview
Cisco ISE solves this by integrating 802.1X or MAB authentication with RADIUS dynamic VLAN assignment. Here’s the flow:
- Endpoint connects to a wired switch port.
- Switch (NAD) sends authentication request to ISE via RADIUS.
- ISE identifies the user/device and matches an Authorization Policy.
- ISE sends a RADIUS Access-Accept with the VLAN ID (via
Tunnel-Private-Group-IDattribute). - Switch reconfigures the port to the assigned VLAN on-the-fly.
- Policy can change dynamically via Change of Authorization (CoA) without disconnecting the port manually.
This enables different VLANs for different identities on the same physical port — e.g., employees get VLAN 20, contractors get VLAN 30, printers get VLAN 50.
Sample Lab Topology
Lab Environment:
- Virtualization: VMware Workstation or EVE-NG
- ISE Server: Cisco ISE 3.x (VM, 4 vCPU, 16 GB RAM)
- Switches: Catalyst 9300/3850 (or IOU L2 in EVE-NG with dot1x support)
- Endpoints:
- Windows 10 laptop (802.1X supplicant)
- Linux box (MAB test)
- Printer/IoT device (MAC Authentication Bypass)
- Management: Cisco DNA Center / CLI (optional)
Topology Description:
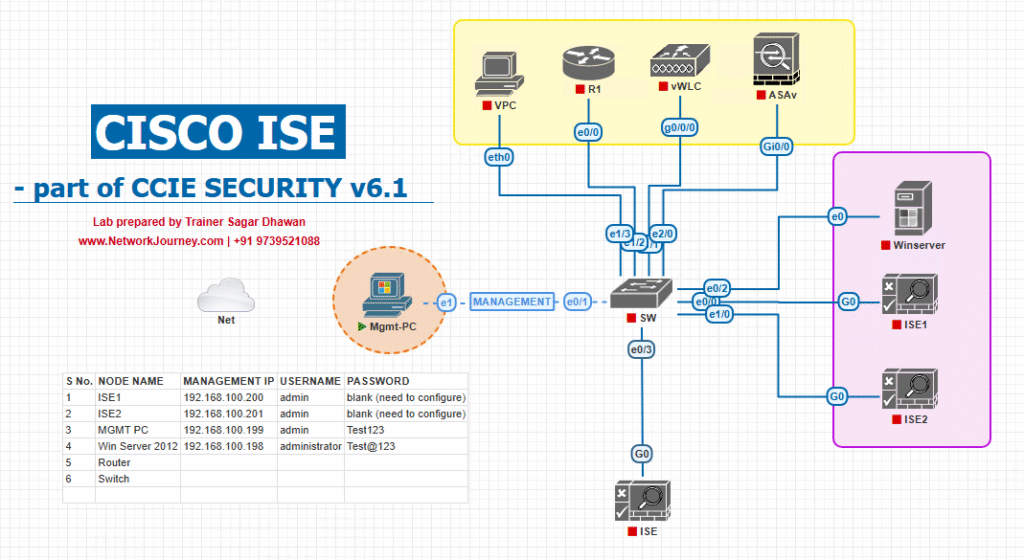
Diagram Placeholder:
[Screenshot: Dynamic VLAN Assignment Topology Diagram with Wired Clients, Switch, ISE, and VLANs]
Step-by-Step GUI & CLI Configuration Guide
Step 1 – Switch Configuration (NAD CLI)
Enable AAA and dot1x on the access switch:
aaa new-model aaa authentication dot1x default group radius aaa authorization network default group radius aaa accounting update periodic 5 radius-server host 10.10.10.50 auth-port 1812 acct-port 1813 key C1sc0ISE ip radius source-interface Vlan1 dot1x system-auth-control interface Gi1/0/10 switchport mode access authentication port-control auto mab dot1x pae authenticator spanning-tree portfast
Step 2 – Create VLANs on the Switch
vlan 20 name Employee_VLAN vlan 30 name Contractor_VLAN vlan 50 name Printer_VLAN
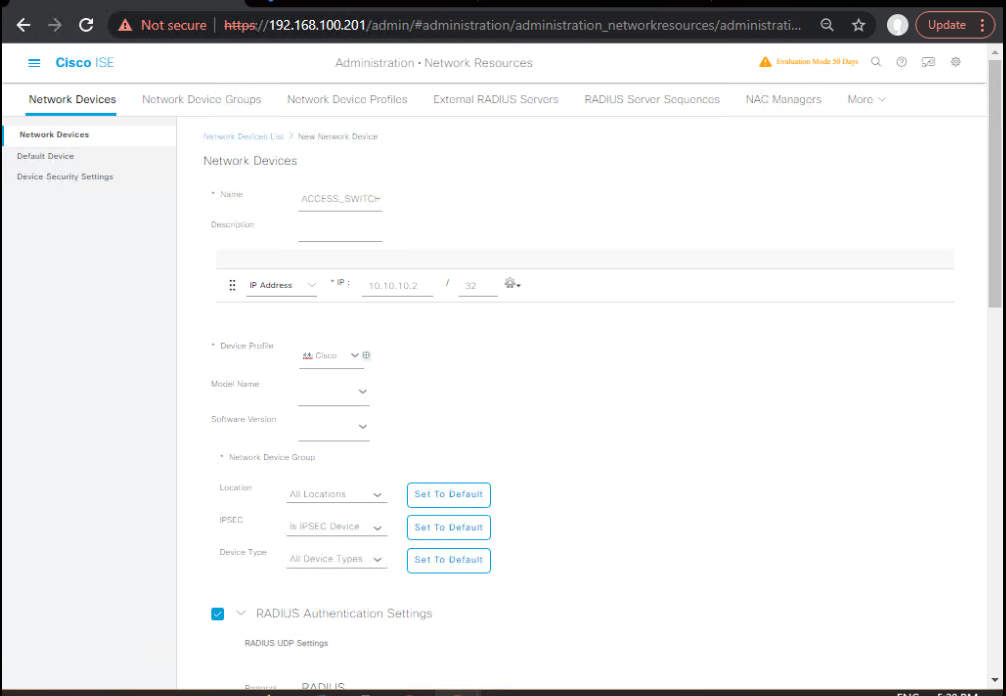
Step 3 – ISE Configuration – Add Switch as NAD
- Navigate to Administration → Network Resources → Network Devices.
- Click Add.
- Name:
Access_Switch_9300 - IP Address:
10.10.10.2 - RADIUS Shared Secret:
C1sc0ISE - [Screenshot: Add NAD in ISE]
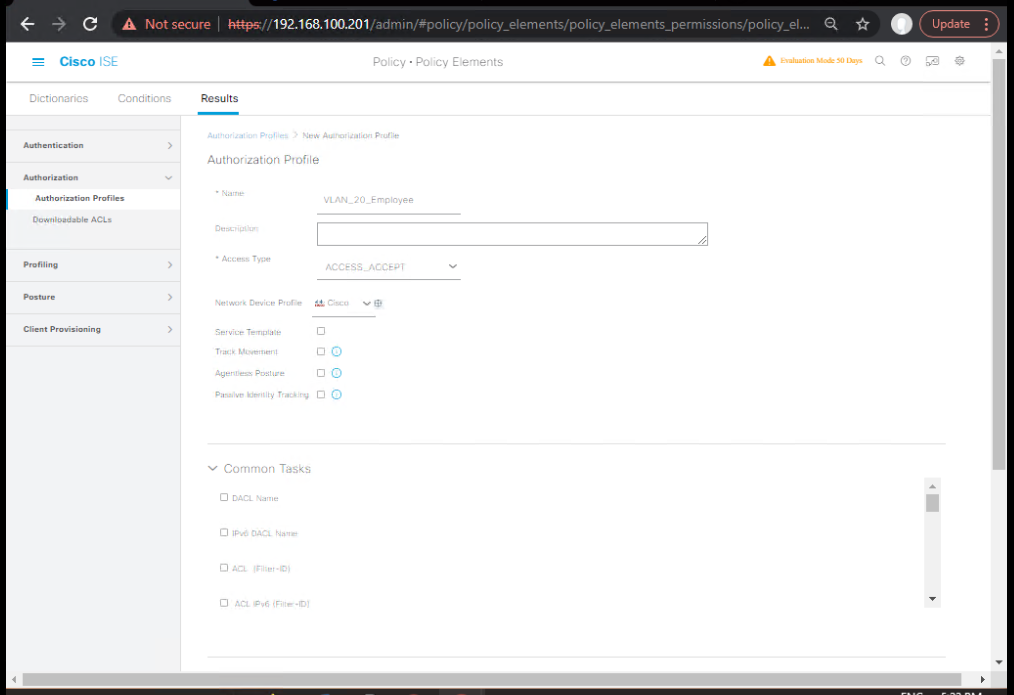
Step 4 – Create Authorization Profiles for VLANs
- Go to Policy → Policy Elements → Results → Authorization → Authorization Profiles.
- Click Add → Name:
VLAN_20_Employee. - Under Common Tasks → VLAN → ID:
20. - Repeat for VLAN 30 and VLAN 50.
- [Screenshot: Authorization Profile VLAN Config in ISE]
Step 5 – Define Authentication Policies
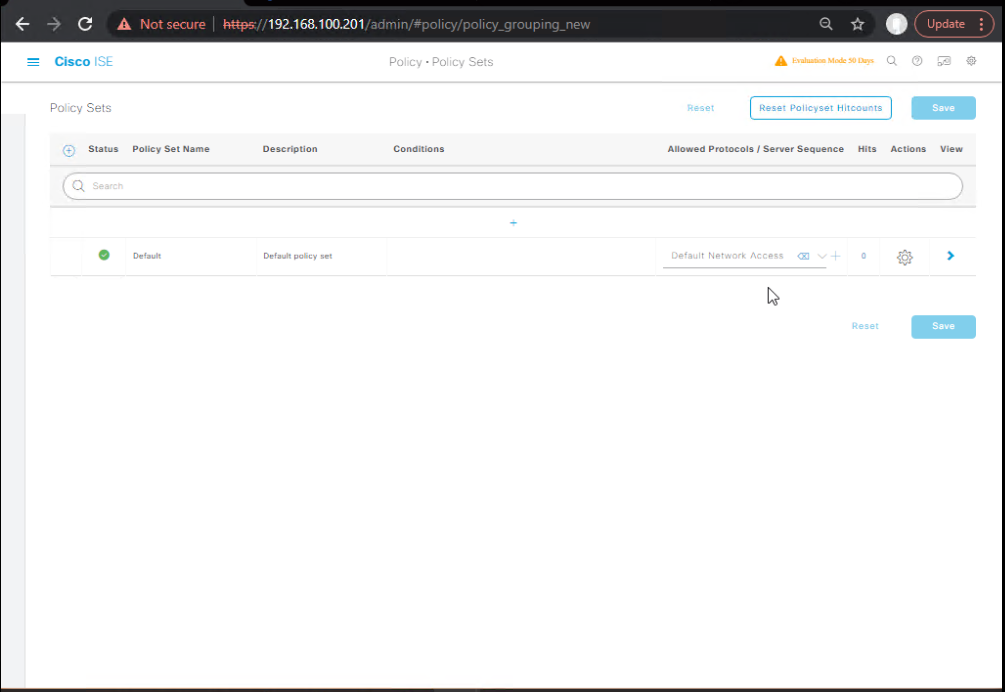
- Navigate to Policy → Policy Sets.
- Select your Wired Policy Set.
- Under Authentication Policy:
- Rule 1:
If Wired_802.1X→ UseAD1(Active Directory). - Rule 2:
If MAB→ UseInternal Endpoints.
- Rule 1:
- [Screenshot: Authentication Policy in ISE]
Step 6 – Define Authorization Policies
- In the same Policy Set, go to Authorization Policy:
- Rule 1:
If AD-User-Group = Employees→ VLAN_20_Employee. - Rule 2:
If AD-User-Group = Contractors→ VLAN_30_Contractor. - Rule 3:
If Endpoint-Group = Printers→ VLAN_50_Printer.
- Rule 1:
- [Screenshot: Authorization Policy VLAN Mapping]
Step 7 – Testing & Validation
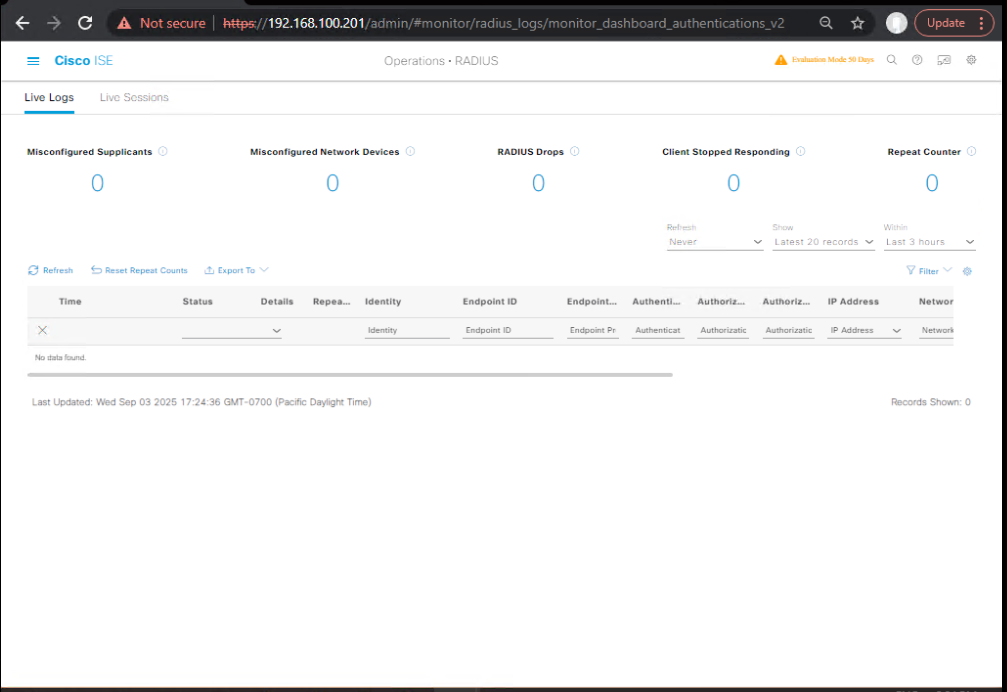
On ISE GUI:
- Navigate to Operations → RADIUS → Live Logs.
- Look for VLAN assignment under Authorization Profile.
- [Screenshot: ISE Live Logs VLAN ID]
On Switch CLI:
show authentication sessions interface Gi1/0/10 details
Look for:
VLAN: 20 Status: Authorized Method: dot1x
Trigger a CoA:
test aaa group radius 10.10.10.50 username user1 password pass1
FAQs: Dynamic VLAN Assignment in Wired Networks
1. What exactly is Dynamic VLAN Assignment in Cisco ISE?
Dynamic VLAN Assignment allows Cisco ISE to assign a VLAN to a wired endpoint dynamically after successful authentication and authorization. Instead of hardcoding VLANs on switch ports, the VLAN is delivered as part of the authorization profile from ISE, enabling user or device-based segmentation.
2. What protocols are used for Dynamic VLAN Assignment?
It typically works with 802.1X or MAB (MAC Authentication Bypass) authentication methods. ISE communicates with the network access device (NAD) via RADIUS and sends VLAN attributes such as:
Tunnel-Type= VLANTunnel-Medium-Type= 802Tunnel-Private-Group-ID= VLAN ID
3. Can a single switch port have multiple VLAN assignments for different users?
Yes, but not simultaneously for multiple devices unless Multi-Auth or Multi-Domain Authentication (MDA) is configured. With single host mode, only one authenticated device is supported per port.
4. What’s the difference between Static VLAN and Dynamic VLAN in wired access?
- Static VLAN: Pre-configured manually on the switch port; doesn’t change unless an admin updates it.
- Dynamic VLAN: Assigned by ISE per authentication event; changes automatically based on policy conditions (user role, device type, posture compliance, time of day, etc.).
5. What happens if Dynamic VLAN assignment fails?
If VLAN assignment fails (e.g., due to an invalid VLAN ID or switch misconfiguration), the port might remain in an unauthorized state, fall into a critical VLAN, or revert to a default VLAN, depending on the switch configuration (authentication event fail settings).
6. How do I verify if Dynamic VLAN assignment worked?
On the switch CLI:
show authentication sessions interface Gi1/0/10 details
Look for:
VLAN: 30(or the VLAN ID assigned by ISE)Session timeoutandStatus: Authz Success
On ISE:
- Check Operations → RADIUS Live Logs for
Tunnel-Private-Group-IDin RADIUS response attributes.
7. Can Dynamic VLAN assignment work with non-802.1X devices?
Yes, using MAB for non-supplicant devices. ISE can still send a VLAN ID based on the MAC address identity group, although security is weaker than 802.1X.
8. Is it possible to assign VLANs based on AD group membership?
Absolutely. Cisco ISE can query Active Directory during authentication and return different VLANs depending on the user’s security group (e.g., Finance gets VLAN 30, HR gets VLAN 40).
9. How does Dynamic VLAN work with Voice + Data VLAN setups?
For IP phones with PCs behind them, VLAN assignment can be handled via Multi-Domain Authentication (MDA) where:
- Voice VLAN is assigned statically on the switch (
switchport voice vlan 20). - Data VLAN for the PC is assigned dynamically via ISE after authentication.
10. What are common misconfigurations that break Dynamic VLAN assignment?
- VLAN not created on the switch or trunk link.
- Trunk allowed VLAN list missing the assigned VLAN.
- Incorrect RADIUS attributes on ISE authorization profile.
authentication opennot configured for certain VLAN failover scenarios.- Access switch running old IOS that doesn’t support dynamic VLAN in 802.1X.
YouTube Link
For more in-depth Cisco ISE Mastery Training, subscribe to my YouTube channel Network Journey and join my instructor-led classes for hands-on, real-world ISE experience
Closing Notes
Dynamic VLAN Assignment in Cisco ISE transforms your wired network into a context-aware access fabric. Instead of static, error-prone port configs, VLANs are tailored per user/device dynamically and securely.
When combined with profiling, posture checks, and CoA, it provides granular, adaptive network segmentation — critical for modern enterprise security.
Upgrade Your Skills – Start Today
If you want to master configurations like Dynamic VLAN Assignment, Posture-based VLANs, and other real-world Cisco ISE deployments, join 4-Month Instructor-Led CCIE Security Mastery Program.
This isn’t theory — you’ll build production-grade lab topologies, tackle enterprise-level NAC scenarios, and get hands-on with troubleshooting so you can deploy ISE with confidence.
Limited Cohorts | Live + Lab-Intensive | CCIE Security Focused
View Full Course Outline & Enroll — Secure your seat before it fills.
Enroll Now & Future‑Proof Your Career
Email: info@networkjourney.com
WhatsApp / Call: +91 97395 21088
![[Day 25] Cisco ISE Mastery Training: Dynamic VLAN Assignment in Wired Networks](https://networkjourney.com/wp-content/uploads/2025/08/Day-25-Cisco-ISE-Mastery-Training-Dynamic-VLAN-Assignment-in-Wired-Networks.png)
![[Day #19 Pyats Series] Introduction to Trigger APIs in pyATS using pyATS for Cisco](https://networkjourney.com/wp-content/uploads/2025/07/Introduction-to-Trigger-APIs-in-pyATS-using-pyATS-for-Cisco.png)
![VRF Lite Explained: Real-World Use Cases, Commands & Troubleshooting [CCNP Enterprise]](https://networkjourney.com/wp-content/uploads/2025/06/VRF-Lite-Explained_networkjourney.png)