Want to Stop Unauthorized Access? SSH and HTTPS Hardening Explained [CCNP ENTERPRISE]
when was the last time you audited your device’s remote access methods?
I still remember the day when a client called me in panic—someone had brute-forced their router via SSH, and guess what? The router had no access-lists, no username policy, and was running outdated SSHv1. Scary, right?
This blog is not just about enabling SSH or HTTPS—it’s about hardening them the way they should be in a real-world enterprise network. We’ll go step-by-step to secure remote access on Cisco devices, from enabling SSHv2 and HTTPS with certificates to locking it down with ACLs and banner warnings.
So buckle up, especially if you’re preparing for CCNA/CCNP or actively managing routers in production—this guide will make you rethink how “secure” your so-called secure access really is.
Table of Contents
Theory in Brief
What is Remote Access Hardening?
Remote access protocols like SSH and HTTPS allow us to manage devices from anywhere. But if left open, they can become easy entry points for attackers. Hardening means strengthening these services to reduce the attack surface.
The Problem
Many networks still:
- Use default usernames/passwords
- Allow access from any source IP
- Run outdated SSH versions (like v1)
- Leave HTTP open alongside HTTPS
- Forget to disable unused access protocols (Telnet, HTTP)
These gaps can allow brute-force attacks, session hijacking, or unauthorized access to config files.
The Solution
Access hardening should include:
- Only enabling secure protocols (HTTPS, SSHv2)
- Disabling insecure ones (Telnet, HTTP)
- Restricting access using IP-based ACLs
- Using strong user authentication
- Customizing port numbers (optional but helpful)
- Applying banners for legal compliance
Security Layers in Access Hardening
- Transport Security – Enforce SSHv2 and HTTPS only
- Access Control – Use ACLs to limit IPs that can connect
- User Authentication – Use local or AAA for login
- Protocol Tuning – Disable HTTP/Telnet and enforce v2
- Legal Notification – Add login banners for security policy
This multi-layered approach makes it much harder for attackers to succeed.
Summary
| Feature | SSH | HTTPS |
|---|---|---|
| Protocol | TCP/22 | TCP/443 |
| Secure Version | SSHv2 | HTTPS (TLS 1.2 or higher) |
| Common Threats | Brute-force, key hijacking | MITM, expired certs |
| Mitigation | ACLs, Strong Auth, Version Lock | CA-Signed Certs, Disable HTTP |
| Cisco Enabling Command | ip ssh version 2 | ip http secure-server |
| Cisco Disable Command | no ip ssh version 1 | no ip http server |
| Best Practice | Use RSA key ≥2048 bits | Use SSL certificates |
CLI Commands
| Task | Command Example | Notes |
|---|---|---|
| Generate RSA Key Pair | crypto key generate rsa modulus 2048 | Needed for SSH and HTTPS |
| Enable SSHv2 | ip ssh version 2 | Use only v2 |
| Disable SSHv1 | no ip ssh version 1 | Remove weak version |
| Create local user | username admin privilege 15 secret Net@1234 | Avoid default/weak passwords |
| Enable AAA (Optional) | aaa new-model | Preferred in enterprise |
| Enable HTTPS | ip http secure-server | Launches HTTPS interface |
| Disable HTTP | no ip http server | Disables unsecure version |
| Restrict access with ACL | access-list 10 permit 192.168.1.0 0.0.0.255line vty 0 4access-class 10 in | Limit access to trusted IPs |
| Add banner | banner login ^C Unauthorized access is prohibited ^C | Adds legal warning |
| Verify SSH | show ip ssh | View SSH version/status |
| Verify HTTPS | show ip http server secure status | Check HTTPS config |
Use Cases
| Scenario | Problem | How Access Hardening Helps |
|---|---|---|
| ISP router exposed to internet | Open SSH and HTTP access from any IP | Apply ACLs to allow only mgmt subnet |
| Government firewall device | Weak login credentials and HTTP enabled | Enforce SSHv2, disable HTTP, use strong secrets |
| NOC team using Telnet | All engineers using telnet across WAN | Disable Telnet and redirect users to SSH |
| Device compromised in audit | No login banner, attacker claims ignorance | Banner shows legal warning and access policy |
LAB – SSH/HTTPS Hardening
LAB TOPOLOGY OVERVIEW
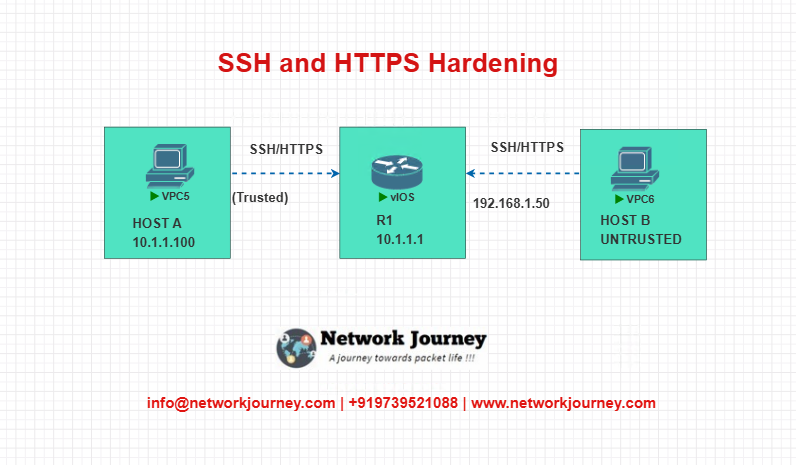
In this EVE-NG lab, we’ll use one Cisco router (R1) and two hosts:
- Host A: Trusted management station
- Host B: Untrusted attacker
CONFIGURATION STEPS
- Create a local user and enable SSHv2
username admin privilege 15 secret Net@1234
ip domain-name netjourney.com
crypto key generate rsa modulus 2048
ip ssh version 2
- Restrict access using ACL
access-list 10 permit 10.1.1.100
line vty 0 4
login local
transport input ssh
access-class 10 in
- Enable HTTPS and disable HTTP
ip http secure-server
no ip http server
- Add a login banner
banner login ^C
Unauthorized access is strictly prohibited.
Monitoring and recording enabled.^C
- Verify settings
show ip ssh
show ip http server secure status
Troubleshooting Tips
| Symptom | Possible Cause | Solution |
|---|---|---|
| SSH not working | RSA key not generated or transport missing | Use crypto key generate rsa and check line vty |
| Access denied from trusted IP | ACL misconfigured | Double-check ACL and access-class command |
| HTTPS page not loading | HTTP not disabled or wrong certificate issue | Use no ip http server and check certificate config |
| Banner not showing | Incorrect delimiter used | Use ^C or consistent special character at start/end |
| SSH version still showing v1 | SSHv2 not enforced | Use ip ssh version 2 and verify again |
FAQs on SSH and HTTPS Access Hardening
1. Why should I disable Telnet and HTTP on Cisco devices?
Answer:
Telnet and HTTP transmit credentials in plain text, making them vulnerable to sniffing attacks. Replacing them with SSH and HTTPS ensures secure, encrypted communication.
2. How do I make sure SSH is using version 2?
Answer:
Use the following command:
ip ssh version 2
Then verify with:
show ip ssh
Ensure it shows “SSH Enabled – version 2.0”.
3. What RSA key length is recommended for SSH?
Answer:
A minimum of 2048 bits is recommended.
Command:
crypto key generate rsa modulus 2048
4. How can I restrict who can SSH into the device?
Answer:
Use an access-list and apply it to the VTY lines:
access-list 10 permit 10.1.1.0 0.0.0.255
line vty 0 4
access-class 10 in
5. How do I check if HTTPS is enabled?
Answer:
Run:
show ip http server secure status
If enabled, it will show:
HTTP secure server status: Enabled
6. What’s the difference between transport input ssh and transport input all?
Answer:
transport input sshallows only SSHtransport input allallows all protocols including Telnet, which is insecure
Always use transport input ssh for secure access.
7. Can I use HTTPS with a self-signed certificate?
Answer:
Yes.
By default, Cisco generates a self-signed certificate when you enable HTTPS:
ip http secure-server
For production, use a CA-signed certificate.
8. How do I create a banner that complies with company policies?
Answer:
Use:
banner login ^C
This system is for authorized use only.
Unauthorized access will be prosecuted.
^C
Replace the message based on your security/legal team’s guidance.
9. What happens if SSH is misconfigured?
Answer:
You may get locked out remotely.
Always test new access policies from a console port or out-of-band method before applying to live routers.
10. Is it okay to use default usernames like “admin”?
Answer:
No.
Default usernames are common brute-force targets. Use unique usernames and strong secrets:
username netadmin privilege 15 secret S3cur3@ccess!
YouTube Video: SSH & HTTPS Hardening Demo
Watch the Complete CCNP Enterprise: Want to Stop Unauthorized Access? SSH and HTTPS Hardening Explained Demo & Explanation on our channel:
Final Note
Understanding how to differentiate and implement Want to Stop Unauthorized Access? SSH and HTTPS Hardening Explained is critical for anyone pursuing CCNP Enterprise (ENCOR) certification or working in enterprise network roles. Use this guide in your practice labs, real-world projects, and interviews to show a solid grasp of architectural planning and CLI-level configuration skills.
If you found this article helpful and want to take your skills to the next level, I invite you to join my Instructor-Led Weekend Batch for:
CCNP Enterprise to CCIE Enterprise – Covering ENCOR, ENARSI, SD-WAN, and more!
Get hands-on labs, real-world projects, and industry-grade training that strengthens your Routing & Switching foundations while preparing you for advanced certifications and job roles.
Email: info@networkjourney.com
WhatsApp / Call: +91 97395 21088
Upskill now and future-proof your networking career!
![Want to Stop Unauthorized Access? SSH and HTTPS Hardening Explained[CCNP ENTERPRISE]](https://networkjourney.com/wp-content/uploads/2025/07/nj-blog-post-ssh-https.jpg)
![DSCP vs CoS & Trust Boundary: Network Marking Demystified for Engineers[CCNP Enterprise]](https://networkjourney.com/wp-content/uploads/2025/07/DSCP-vs-CoS-Trust-BoundaryNetwork-Marking-Demystified-for-Engineers_networkjourney.png)
![Two-Tier vs Three-Tier Network Architecture – Complete Guide with EVE-NG Lab & CLI [CCNP Enterprise]](https://networkjourney.com/wp-content/uploads/2025/06/Two-Tier-vs-Three-Tier-Network-Architecture_networkjourney-1.png)
![Overlay Technologies for CCNP Enterprise: The Complete 2025 Guide with Labs, CLI & Exam Relevance [CCNP ENTERPRISE]](https://networkjourney.com/wp-content/uploads/2025/06/Overlay-Technologies-for-CCNP-Enterprise_networkjourney.png)