[Day 11] Cisco ISE Mastery Training: Understanding AAA & RADIUS Basics
Table of Contents
Introduction
AAA (Authentication, Authorization, Accounting) + RADIUS are the foundation of modern Network Access Control. In Cisco ISE deployments, AAA controls who gets on the network (Authentication), what they can do (Authorization), and what they did (Accounting). RADIUS is the protocol that transports AAA messages between Network Access Devices (NADs) — switches, WLCs, VPN gateways — and ISE.
For a NAC engineer, understanding AAA flows, RADIUS packet types (Access-Request, Challenge, Accept/Reject, Accounting), attributes (AVPs), and how ISE processes them is essential. This lesson gives you the theory only when necessary, and otherwise focuses on the exact lab tasks and CLI/GUI checks you’ll perform to prove AAA works end-to-end.
Problem Statement
Common real-world challenges that this lesson solves:
- Engineers see authentication failures but can’t tell whether the problem is network, RADIUS, policy, or identity store related.
- NADs are configured to talk to ISE but produce no Live Log entries (so you don’t know if RADIUS even arrived).
- Authorization results are wrong (user gets wrong VLAN or dACL).
- Accounting is missing — audits and troubleshooting lack the session trail.
You’ll learn how to clearly separate layers (connectivity, protocol, identity, policy) and validate each with specific CLI and GUI commands so you can quickly troubleshoot real issues.
Solution Overview
We use repeatable lab checks and validation steps:
- Configure a simple AAA/RADIUS flow: Switch → ISE (RADIUS auth/account).
- Observe the RADIUS message exchange with ISE Live Logs and packet captures.
- Validate authentication (user credentials), authorization (VLAN/dACL assignment), and accounting records.
- Use device debug/test commands and ISE CLI to pinpoint failures (shared secret, IP mismatch, identity lookup, EAP issues).
By the end you’ll be able to answer: Did the packet reach ISE? Which policy matched? Why was this user accepted or rejected?
Sample Lab Topology
Platform: VMware ESXi or EVE-NG
Nodes / IPs
- ISE (PAN+PSN) —
ise.lab.local→10.10.10.5 - Switch (IOSv-L2 / Catalyst) —
sw-lab-01→10.10.10.2 - Windows AD (optional) —
ad.lab.local→10.10.10.10 - Windows Client (wired) — DHCP / test user
alice - WLC (optional) —
10.10.10.20(for wireless EAP testing)
Topology Layout:
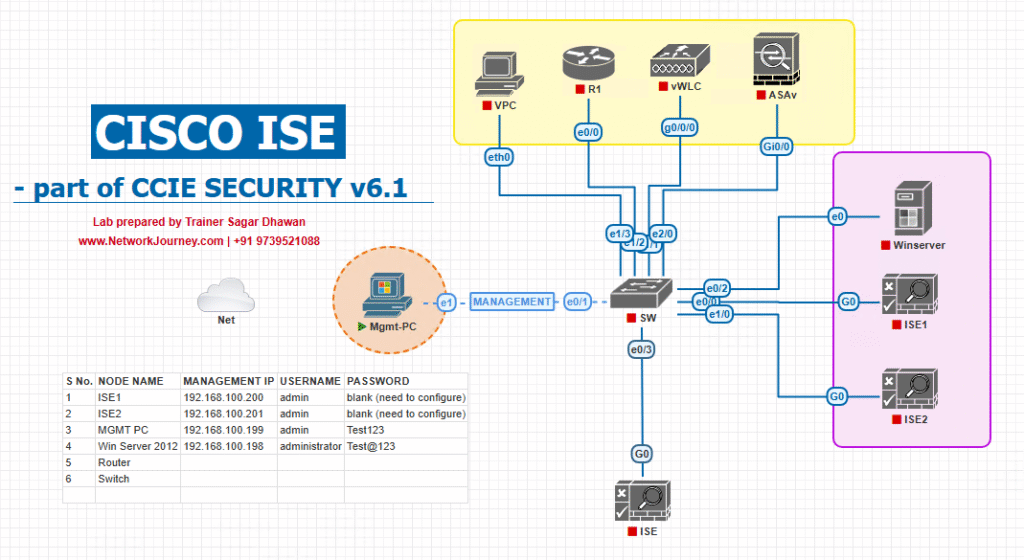
Notes: ISE & NADs must have correct DNS/NTP and routing. Use static IPs for ISE and NAD management.
Step-by-Step GUI Configuration Guide (with CLI validation)
PRE-CHECKS (console on ISE)
Run these before any AAA test:
ise/admin# ping 10.10.10.2 ise/admin# ping 10.10.10.10 # if AD in lab ise/admin# nslookup ad.lab.local 10.10.10.10 ise/admin# show ntp status ise/admin# show application status ise
Expected: ping/lookup succeed; NTP synced; ISE services Running.
Step 1 — Understand the AAA Flow (quick theory for your lab)
- Authentication = NAD asks ISE: “Who is this user?” (RADIUS Access-Request → Access-Accept/Reject/Challenge).
- Authorization = ISE answers: “What VLAN/ACL should this user get?” (returned in Access-Accept attributes like Tunnel-Private-Group-ID, Filter-ID, dACL).
- Accounting = NAD sends start/stop usage info to ISE (Accounting-Request/Response) for logging.
Keep that flow in mind as you run tests.
Step 2 — Add the Switch to ISE (GUI)
- ISE GUI:
Administration → Network Resources → Network Devices → Add.
[Screenshot: ISE Add Network Device Screen]
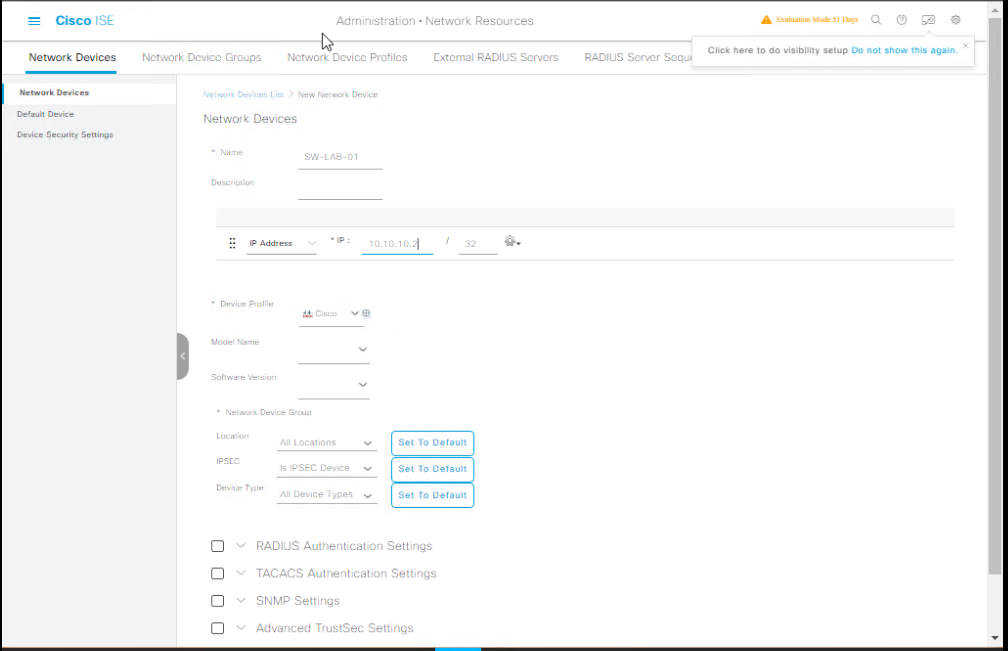
- Fill:
- Name:
SW-Lab-01 - IP Address:
10.10.10.2 - Device Type:
Switch - Shared Secret:
c1sc0Lab$ecret! - Device Group:
Switches-Lab(create if not present) - Save.
- Name:
ISE Validation (GUI): Network device entry shows in list. Click the device → verify IP and that RADIUS Authentication is enabled.
Step 3 — Configure RADIUS on the Switch (IOS syntax examples)
Modern IOS (radius server object):
conf t radius server ISE address ipv4 10.10.10.5 auth-port 1812 acct-port 1813 key c1sc0Lab$ecret! aaa new-model aaa group server radius ISE-GROUP server name ISE aaa authentication dot1x default group ISE-GROUP aaa authorization network default group ISE-GROUP dot1x system-auth-control interface Gi1/0/10 switchport mode access switchport access vlan 1 authentication port-control auto dot1x pae authenticator mab spanning-tree portfast exit
Legacy IOS (radius-server host):
conf t radius-server host 10.10.10.5 auth-port 1812 acct-port 1813 key c1sc0Lab$ecret! aaa new-model ...
Switch Validation (CLI):
show running-config | section radius show aaa servers show dot1x all
Step 4 — Create a Simple Authentication Policy in ISE (GUI)
- ISE GUI:
Policy → Policy Sets. Open (or create) aLabpolicy set.
[Screenshot: ISE Policy Set Screen]
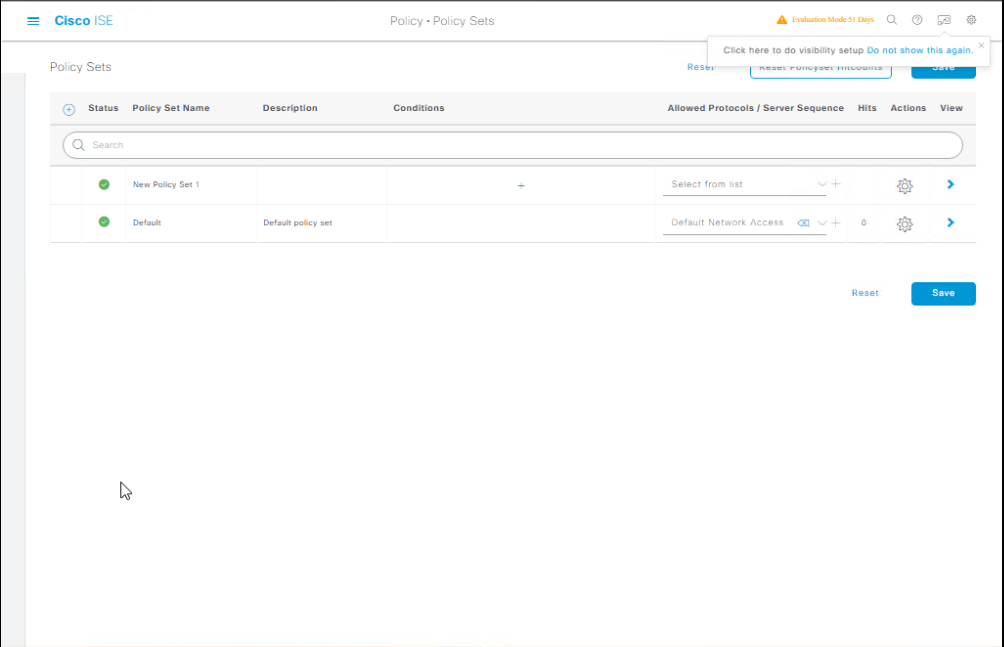
- Authentication Policy: Add rule:
- Condition:
If Called-Station-Id starts with <your-switch-id>or simpleAnyfor lab. - Action: Use Identity Source: Internal Users (or AD if integrated).
- Save.
- Condition:
- Authorization Policy:
- Add rule: Condition:
Authenticated Identity→Internal Users: lab-usersorAD group: Employees - Result: Authorization Profile →
Permit-VLAN-100(configure an Authorization Profile that sets VLAN=100 or dACL).
[Screenshot: Policy → Authorization Rule]
- Add rule: Condition:
ISE Validation (GUI): Policy set shows the rules. You can simulate authentication in GUI (Test) or run real tests from switch/client.
Step 5 — Test Authentication (trigger from switch/client)
A. Simulate with switch (if supported)
test aaa group radius ISE-GROUP username alice password AliceP@ss new-code
OR for legacy:
test aaa-server authentication 10.10.10.5 1812 username alice password AliceP@ss
B. Real test: Connect the Windows client to the switch port (Gi1/0/10) — attempt 802.1X/PEAP login or physical reconnection to trigger MAB.
Switch CLI validation:
show authentication sessions interface Gi1/0/10 show dot1x all
ISE GUI validation:
Operations → RADIUS → Live Logs— filter byClient(switch IP) orUser(alice).- Look for sequence: Access-Request → (if PEAP) Access-Challenge → Access-Accept OR Access-Reject.
[Screenshot: ISE Live Logs showing Access-Request → Access-Accept]
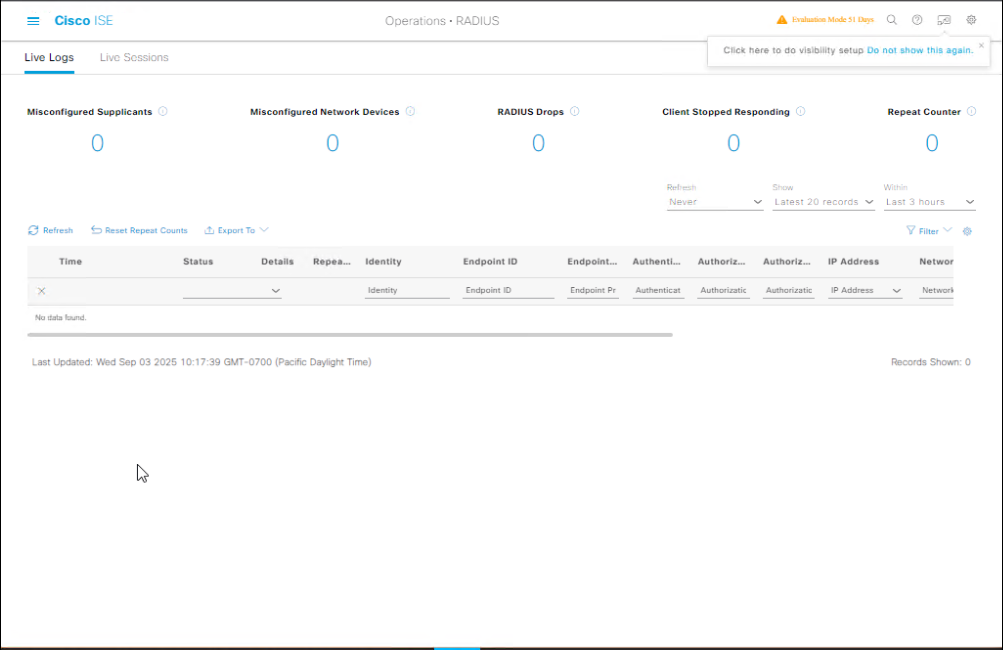
Key: Live Logs shows Identity Source used, which Authorization Profile was applied, and attributes returned.
Step 6 — Validate Authorization Attributes (what ISE returned)
In Live Logs click the Accept entry → view details:
- Authentication result (Success/Fail)
- Authorization result: check VLAN assigned (Tunnel-Private-Group-ID), dACL, Filter-ID.
- On switch, ensure session reflects assigned VLAN or applied ACL.
Switch CLI:
show authentication sessions interface Gi1/0/10 show mac address-table interface Gi1/0/10
If VLAN assignment uses dynamic VLAN (tunnel), the switch output shows assigned VLAN.
Step 7 — Validate Accounting (optional but important)
- Ensure the switch is configured to send accounting (we set acct-port 1813 earlier).
- Trigger session start and stop (connect / disconnect client).
- In ISE GUI:
Operations → RADIUS → Live LogsorReports → Accountingview records.
Switch CLI:
show accounting
Step 8 — Packet Capture & Deep Troubleshooting
If Live Logs show nothing, capture packets on the ISE management interface:
On ISE (lab safe only):
ise/admin# tcpdump -i eth0 'udp port 1812 or udp port 1813' -w /tmp/radius.pcap # copy file off and open in Wireshark
What to look for in pcap:
- Is Access-Request arriving? (Yes → check ISE logs for policy match.)
- If requests arrive but ISE does not respond, check
show application status ise. - If Access-Request contains unexpected attributes, check NAD configuration and RADIUS formatting.
Step 9 — Common Quick Checks & Fixes (troubleshooting checklist)
- No Live Log entry: verify NAD source IP matches ISE entry, confirm UDP 1812/1813 not blocked, check NAT/translations.
- Access-Reject / Wrong reason: open Live Log entry → check Reason (bad password, no identity source match).
- “Client not found”: switch source IP differs or secret mismatch; check ISE Network Device entry.
- EAP issues: check TLS certs (EAP-TLS), ensure clients trust CA, check EAP methods in authentication policy.
- Accounting missing: verify accounting port configured and NAD sends Accounting-Start/Stop.
Step 10 — Harden & Best-Practice Settings
- Use UDP 1812/1813 (modern standard).
- Use strong shared secrets and store them securely.
- Configure RADIUS timeout/retries on NAD (example: timeout 5 retries 3).
- Add multiple ISE PSNs for redundancy in device config (use server group).
- Monitor Live Logs and set alarms for repeated rejects.
FAQs
1. What does AAA stand for, and why is it important in Cisco ISE?
AAA stands for Authentication, Authorization, and Accounting.
- Authentication confirms the identity of a user/device.
- Authorization determines what that user/device can access.
- Accounting logs and tracks user activity.
In Cisco ISE, AAA forms the foundation for secure access control in NAC (Network Access Control) deployments.
2. What is the difference between RADIUS and TACACS+ in Cisco ISE?
- RADIUS is used for network access authentication (802.1X, MAB, VPN) and carries authentication + authorization in a single packet flow.
- TACACS+ (though not natively handled by ISE) is typically used for administrative access to network devices and separates authentication, authorization, and accounting.
ISE mainly operates with RADIUS for endpoint access control.
3. Does Cisco ISE support both PAP, CHAP, and EAP authentication methods?
Yes.
- PAP/CHAP are used in some legacy or simple NAC scenarios.
- EAP (EAP-TLS, PEAP, EAP-FAST) is the preferred method for secure 802.1X deployments in enterprise environments.
4. How does RADIUS integrate with Cisco ISE in real-world deployments?
Cisco ISE acts as a RADIUS server.
When a switch/WLC receives an access request, it sends the request to ISE via RADIUS. ISE evaluates the request against policies (policy sets, authentication & authorization rules) and responds with access acceptance, rejection, or challenge.
5. What UDP ports must be opened for RADIUS communication with Cisco ISE?
By default:
- UDP 1812 → Authentication
- UDP 1813 → Accounting
(Some devices use 1645/1646 for legacy compatibility, but 1812/1813 is recommended.)
6. Can ISE handle both wired and wireless AAA with the same RADIUS configuration?
Yes. You can configure both wired switches and WLCs as network devices in ISE with shared RADIUS secrets. The same ISE instance can authenticate users across both mediums, provided your policy sets are correctly configured.
7. How do I test RADIUS connectivity between a network device and ISE?
- From the switch/WLC CLI: Use
test aaa group radius <username> <password> new-code - From ISE GUI: Go to Administration → Network Resources → Network Devices, select the device, and use the Test AAA option.
- Always check ISE Live Logs for the request and result.
8. What happens if RADIUS authentication fails in ISE?
- The device may fall back to MAB (MAC Authentication Bypass) if configured.
- The failure could be due to wrong shared secret, incorrect IP address, mismatched authentication protocol, or unreachable ISE node.
- Use ISE Live Logs and RADIUS debug on the switch/WLC to troubleshoot.
9. How do accounting logs in ISE help in security audits?
Accounting logs track user session details: login/logout time, IP addresses, endpoints used, and the amount of data transferred. This helps with:
- Forensics after a security incident
- Compliance for regulatory audits
- User behavior analysis in enterprise environments
10. Can ISE integrate with an external RADIUS server?
Yes. ISE can act as:
- RADIUS proxy → Forward requests to another RADIUS server.
- RADIUS client → Use external AAA servers for authentication while still applying its own policies.
YouTube Link
For more in-depth Cisco ISE Mastery Training, subscribe to my YouTube channel Network Journey and join my instructor-led classes for hands-on, real-world ISE experience
Closing Notes (Key takeaways)
- AAA is three separate concerns — authenticate, authorize, account — and each must be validated independently.
- Use ISE Live Logs as your primary debugging tool for RADIUS flows; it tells you identity source, policy match, and returned attributes.
- Always validate connectivity (ping, DNS, NTP), RADIUS reachability (UDP 1812/1813), and shared secret alignment before chasing policy issues.
- Packet captures and device
test aaacommands are your fastest way to determine whether a packet reached ISE and how it was processed. - For scale and reliability, configure multiple RADIUS servers, server groups on NADs, and use secure, rotated secrets.
Fast-Track to Cisco ISE Mastery Pro
For more in-depth Cisco ISE Mastery Training, subscribe to my YouTube channel Network Journey and join my instructor-led classes.
Want to turn these lab skills into a career-level edge? I run a 4-month, instructor-led CCIE Security & ISE Mastery program that includes:
- Weekly live labs (VMware ESXi & EVE-NG), deep AAA/RADIUS troubleshooting sessions, and graded lab tasks.
- 1:1 doubt sessions, lab correction feedback, and exam-style scenarios.
- A free eligibility + lab review call for qualified applicants (we review your lab topology and recommend the right batch).
- Limited seats per batch to keep instruction hands-on.
Reserve your free eligibility call & join the waitlist:
https://course.networkjourney.com/ccie-security/
(Enroll Now & Future‑Proof Your Career)
Email: info@networkjourney.com
WhatsApp / Call: +91 97395 21088
![[Day 23] Cisco ISE Mastery Training: Guest VLAN & Critical VLAN Configuration](https://networkjourney.com/wp-content/uploads/2025/08/Day-23-Cisco-ISE-Mastery-Training-Guest-VLAN-Critical-VLAN-Configuration.png)
![[Day 37] Cisco ISE Mastery Training: Wired Redirection for Non‑Compliant Devices](https://networkjourney.com/wp-content/uploads/2025/08/Day-37-Cisco-ISE-Mastery-Training-Wired-Redirection-for-Non‑Compliant-Devices.png)
![[Day 22] Cisco ISE Mastery Training: MAB (MAC Authentication Bypass) Configuration](https://networkjourney.com/wp-content/uploads/2025/08/Day-22-Cisco-ISE-Mastery-Training-MAB-MAC-Authentication-Bypass-Configuration.png)